Interpretation of the Management Measures for Compliance Audit of Personal Information Protection - Feeling the Rhythm and Rhythm of Regulatory Flow
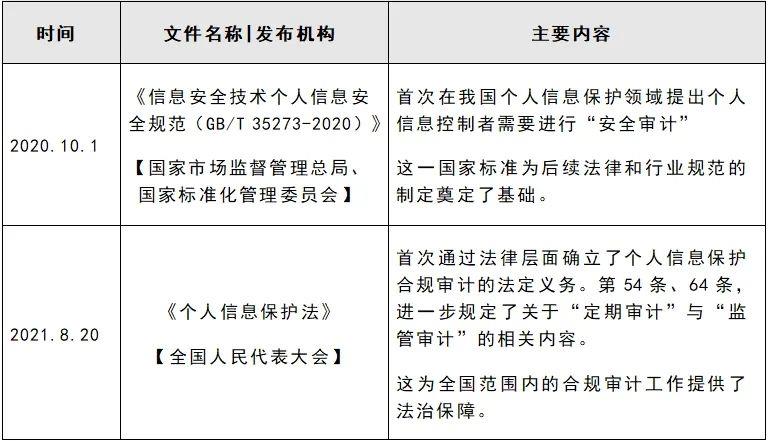
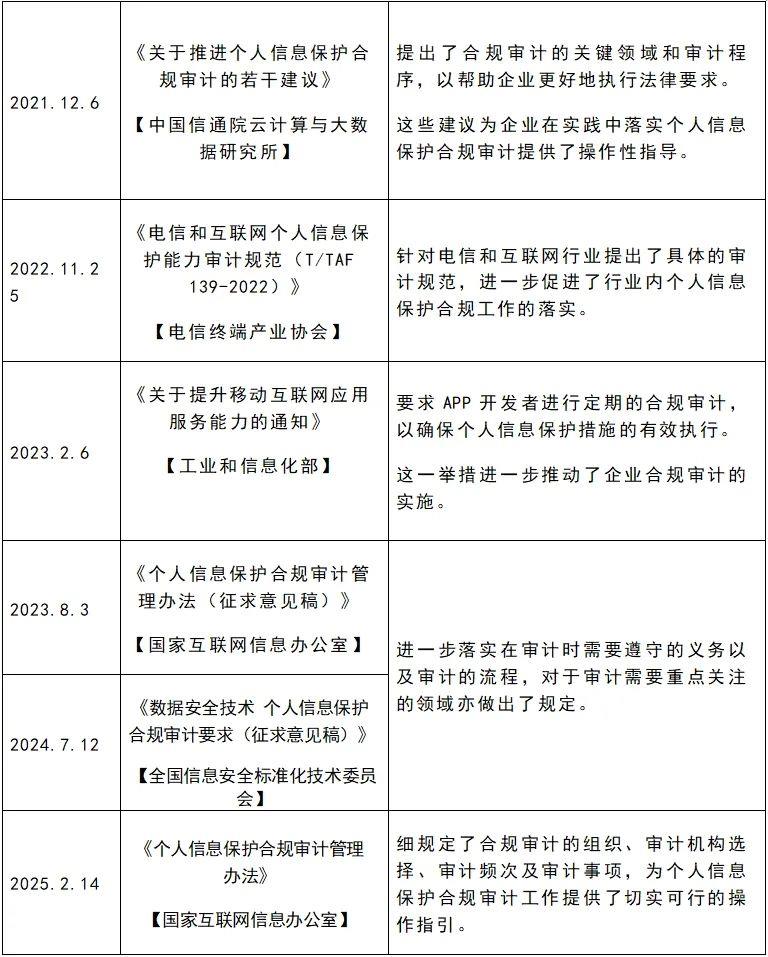
Regarding personal information compliance audit, Articles 54 and 64 of the Personal Information Protection Law establish the obligation of personal information processors to undertake personal information protection compliance audit, and respectively stipulate two triggering situations for personal information protection compliance audit, namely that personal information processors should regularly conduct compliance audits on their processing of personal information in accordance with laws and administrative regulations ("regular audits"), and departments fulfilling personal information protection responsibilities may require personal information processors to entrust professional institutions to conduct compliance audits on their personal information processing activities ("regulatory audits") if they find that there are significant risks or personal information security incidents in their personal information processing activities during the performance of their duties. Article 27 of the Regulations on the Administration of Network Data Security once again reaffirms the obligation of personal information processors to conduct independent audits, and clarifies that personal information processors may conduct compliance audits on their own or by entrusting professional institutions. In August 2023, the State Internet Information Office issued the Administrative Measures for Personal Information Protection Compliance Audit (Draft for Comments); On July 12, 2024, the National Information Security Standardization Technical Committee released the national standard "Data Security Technology Personal Information Protection Compliance Audit Requirements (Draft for Comments)". This article aims to comprehensively review and interpret the official draft of the Audit Measures.
1、 Background of the Implementation of the Management Measures for Compliance Audit of Personal Information Protection
2、 Key changes in the comparison between the official draft of the Audit Measures and the draft for soliciting opinions
(1) Distinguish the scope of audit subjects and adjust the audit frequency
The official draft of the "Audit Measures" has clearly distinguished the scope of audit subjects. In response to the regular audit obligations of personal information processors, the official draft has adjusted the triggering conditions based on the scale of personal information processing. Specifically, personal information processors who only process personal information of over 10 million people are required to conduct a personal information protection compliance audit at least once every two years.
Other personal information processors who have not reached a specific scale will no longer be subject to mandatory audit frequency requirements, and can flexibly decide the audit frequency according to their own actual situation, and can choose to voluntarily conduct audits. For the same matter or risk, the formal draft stipulates that personal information processors shall not be required to conduct duplicate audits. This adjustment constrains the administrative power in auditing and reduces the audit responsibility of enterprises.
Draft Opinion:
Personal information processors who handle personal information of over one million people shall conduct at least one personal information protection compliance audit annually; Other personal information processors shall conduct a personal information protection compliance audit at least once every two years.
Official draft:
Personal information processors who handle personal information of over 10 million people shall conduct a personal information protection compliance audit at least once every two years.
[New] For the same personal information security incident or risk, it is not allowed to repeatedly require personal information processors to entrust professional institutions to conduct personal information protection compliance audits.
(2) Further refinement of audit triggering conditions
The official draft of the "Audit Measures" provides a detailed list of the triggering conditions for audits. Compared to the opinions in the draft that state "there are significant risks" or "personal information security incidents occur", the "Audit Measures" provide clearer references for both protection departments and enterprises, which helps regulatory authorities to fulfill their responsibilities more reasonably.
Draft Opinion:
If the department responsible for personal information protection discovers that there are significant risks in personal information processing activities or personal information security incidents occur during the performance of its duties, it may require the personal information processor to entrust a professional organization to conduct compliance audits on its personal information processing activities.
Official draft:
If a personal information processor falls under any of the following circumstances, the national cyberspace administration and other departments responsible for personal information protection (hereinafter collectively referred to as the protection departments) may require the personal information processor to entrust a professional organization to conduct compliance audits of personal information processing activities:
(1) Discovering significant risks such as serious impact on personal rights or lack of security measures in personal information processing activities;
(2) Personal information processing activities may infringe upon the rights and interests of numerous individuals;
(3) A personal information security incident occurs, resulting in the leakage, tampering, loss, or damage of personal information of more than 1 million people or sensitive personal information of more than 100000 people.
(3) Selection and Management of Professional Institutions
1. Delete the recommended directory and specify the requirements for professional institutions
In the draft opinion, it is stipulated to establish a recommended directory of professional institutions for personal information protection compliance auditing, and encourage personal information processors to prioritize selecting professional institutions in the recommended directory to carry out personal information protection compliance auditing activities. The Audit Measures have removed clauses related to recommended directories and made provisions on the professional ethics required by professional institutions.
Draft Opinion:
The national cyberspace administration department, together with relevant departments of the State Council such as public security organs, shall establish a recommended directory of professional institutions for personal information protection compliance audit in accordance with the principles of overall planning, rational layout, and selective recommendation. They shall organize annual evaluations and assessments of professional institutions for personal information protection compliance audit, and dynamically adjust the recommended directory of professional institutions for personal information protection compliance audit based on the evaluation results.
Encourage personal information processors to prioritize selecting professional institutions in the recommended directory to conduct personal information protection compliance audits.
Official draft:
Professional institutions should have the ability to conduct personal information protection compliance audits, with audit personnel, venues, facilities, and funds that are suitable for their services.
Encourage relevant professional institutions to obtain certification. The certification of professional institutions shall be carried out in accordance with the relevant provisions of the Certification and Accreditation Regulations of the People's Republic of China.
2. Add an independent obligation for institutions, stipulating that institutions need to have objectivity
The official draft of the "Audit Measures" further strengthens the independence constraint mechanism of professional institutions, expanding the scope of obligation subjects from the professional institutions themselves to their affiliated institutions and the same audit project leader. Based on the principle of "auditors should be independent of the audited party and have no interest relationship" clearly stated in the "Data Security Technology Personal Information Protection Compliance Audit Requirements (Draft for Comments)", it can be seen that the current rules have significantly increased the regulatory strength for the independence of audit activities. In response to the issue of continuity in audit services, the official draft adopts the expression of "three or more times" instead of the original clause. According to the relevant legislative interpretation rules [Legislative Technical Specifications (Trial) (1)], the definition standard of "more than" includes this number. It can be inferred that the maximum number of times the same audit institution, its affiliates, and project leaders can conduct audits on the same object continuously is two times. This technical adjustment avoids the independence risk caused by long-term binding from the institutional level.
Draft Opinion:
Professional organizations conducting personal information protection compliance audits should maintain independence and objectivity, and conduct no more than three consecutive personal information protection compliance audits for the same audit subject.
Official draft:
The same professional institution and its affiliated institutions, as well as the same compliance audit leader, shall not conduct personal information protection compliance audits on the same audit object for more than three consecutive times.
3. Increase other related obligations of the institution
The official draft of the "Audit Measures" has accurately defined the confidentiality responsibilities of professional institutions, stipulating that professional institutions need to protect personal information, trade secrets, and other information. According to the official draft, professional institutions must independently complete all audit processes and are prohibited from delegating authorization to third parties for operation. This type of regulation not only strengthens the confidentiality standards in the audit process, but also clarifies from a legal perspective that the act of personal information processors providing data to the auditing party constitutes a delegation relationship. Accordingly, before initiating a compliance audit, audit institutions must strictly follow the mandatory provisions of Article 55 of the Personal Information Protection Law and complete the personal information protection impact assessment procedure.
Draft Opinion:
Professional organizations engaged in personal information protection compliance auditing activities should make professional judgments on compliance auditing with integrity, fairness, and objectivity.
Professional institutions are not allowed to subcontract and entrust third parties to conduct personal information protection compliance audits.
The information obtained by professional institutions in fulfilling their responsibilities of personal information protection compliance audit can only be used for the needs of personal information protection compliance audit and cannot be used for other purposes; Professional institutions should assume confidentiality responsibilities for the information obtained; Professional institutions should take corresponding technical and other necessary measures to ensure data security.
Professional organizations shall not maliciously interfere with the normal business activities of personal information processors when fulfilling their compliance audit responsibilities for personal information protection.
If professional institutions issue false or untrue reports and other violations, personal information processors and related parties may file complaints with the department responsible for personal information protection. If verified by the department responsible for personal information protection, it will be permanently prohibited from being included in the recommended directory of professional institutions for personal information protection compliance audit.
Official draft:
Professional organizations engaged in personal information protection compliance audit activities shall comply with laws and regulations, make professional judgments on compliance audit with integrity, fairness and objectivity, and shall keep confidential personal information, trade secrets, confidential business information, etc. obtained in the performance of personal information protection compliance audit duties in accordance with the law. They shall not disclose or illegally provide them to others, and shall promptly delete relevant information after the completion of compliance audit work.
Professional institutions are not allowed to entrust other institutions to conduct personal information protection compliance audits.
(4) Clear regulatory audit requirements
According to Article 52 of the Personal Information Protection Law, which stipulates the need to appoint dedicated protection personnel for processing large amounts of personal information, the official draft of the Audit Measures clearly stipulates that personal information processors who handle personal information of more than one million people should appoint dedicated personnel to be responsible for personal information protection compliance audit work. When entrusting external audits, they must fulfill their obligation to cooperate and supervise rectification. The accompanying "Guidelines for Compliance Audit of Personal Information Protection" ("Audit Guidelines") provide detailed regulations on the qualification admission standards (such as professional background, length of service) and core functional areas (including risk assessment authority, rectification suggestion authority, etc.) of personnel in this position.
Official draft:
[New] Personal information processors who handle personal information of more than 1 million people shall designate a personal information protection responsible person to be responsible for the compliance audit of personal information protection of personal information processors.
Personal information processors who provide important Internet platform services, have a large number of users, and have complex business types should establish independent institutions mainly composed of external members to supervise the compliance audit of personal information protection.
(5) Regular auditing institutions and audit supervision
The official draft of the "Audit Measures" strengthens the full chain supervision of compliance audit activities by introducing a dual constraint mechanism of regulatory authorities' normalized verification system and social supervision feedback channels. It should be noted that, according to the statutory responsibilities of the "Administrative Law Enforcement Procedures for Cyberspace Departments", cyberspace institutions have the obligation to investigate complaints, appeals, or reports from natural persons, legal persons, and other organizations in a timely manner; According to the relevant judicial interpretations of the Supreme People's Court (Article 12 of the Judicial Interpretation of the Administrative Litigation Law), complainants with vested interests may claim their rights through administrative reconsideration or administrative litigation in accordance with the law. This institutional design essentially incorporates corporate audit compliance disputes into the framework of administrative relief procedures. The potential high procedural expenses and public opinion risks create a coercive effect, prompting personal information processors to prudently fulfill their audit obligations to avoid derivative legal disputes.
Official draft:
[New] The protection department shall supervise and inspect the compliance audit of personal information protection conducted by personal information processors.
Any organization or individual has the right to file complaints and reports to the protection department regarding illegal activities in the compliance audit of personal information protection. The department receiving complaints or reports shall handle them in a timely manner in accordance with the law, and inform the complainant or informant of the results of the handling.
(6) Main changes in the Audit Guidelines
1. In line with the promulgation of the "Regulations on Promoting and Regulating Cross border Data Flow", the key review items for the compliance audit of personal information export have been updated.
2. Considering the practical difficulties faced by personal information processors in conducting audits on recipients when they entrust the processing, transfer, or provision of personal information to other personal information processors, the "Audit Guidelines" have completely removed the review items for recipients.
The Audit Guidelines basically cover all key compliance concerns related to personal information processing. In addition to serving the compliance audit work of personal information protection, they can also serve as a reference for daily business operation compliance. However, it should also be noted that the "Audit Guidelines" are only guidelines for professional institutions to focus on compliance matters. Enterprises should still fulfill their personal information protection compliance obligations in accordance with the comprehensive provisions of the Personal Information Protection Law.
In addition, on July 12, 2024, the National Network Security Standardization Technical Committee issued a draft for soliciting opinions on the national standard "Data Security Technology Personal Information Protection Compliance Audit Requirements", which has more detailed requirements for the process, implementation requirements, and other matters of personal information protection compliance audit. The appendix also provides the draft template and report template for the audit report, which can be used as a reference for personal information processors and professional institutions when conducting audit work.
3、 The main content of the official draft of the Audit Measures
(1) Two scenarios for conducting audits
According to the Audit Measures, enterprises that need to be reviewed are mainly divided into two categories: those that meet the conditions and need to conduct their own reviews (self audit), and those that conduct reviews in accordance with the requirements of the national cyberspace administration and other departments responsible for personal information protection (regulatory audit).
1. Self audit/regular audit
Self audit/regular audit refers to the process by which personal information processors are required by law to conduct regular compliance audits of their processing of personal information in compliance with laws and administrative regulations, either through internal institutions or commissioned professional organizations.
2. Regulatory audit
Regulatory audit refers to the situation where the national cyberspace administration and other departments responsible for personal information protection (hereinafter collectively referred to as protection departments) may require personal information processors to entrust professional institutions to conduct compliance audits on their personal information processing activities if they have serious impacts on personal rights, may infringe on the rights of multiple people, or have major security incidents.
(2) Audit frequency
The Audit Measures classify personal information processors into two categories based on the scale of information processing, resulting in differences in audit frequency.
Personal information processors who handle personal information of over 10 million people shall conduct a personal information protection compliance audit at least once every two years.
Personal information processors who handle personal information not exceeding 10 million may decide on their own whether to conduct compliance audits and the frequency of compliance audits based on actual circumstances.
(3) Audit content
In the "Audit Guidelines", a detailed list of key issues that need to be reviewed is provided, including the legality basis of the audit, the handling of personal information of minors under the age of 14, and the handling of sensitive personal information, totaling 27 items. This article summarizes the key review points listed in the Audit Guidelines based on their content, as follows:
1. Regarding the Basis of Legitimacy
(1) Legitimacy basis: The focus is on reviewing whether individuals have obtained voluntary and explicit consent with full knowledge, whether consent has been obtained again when the purpose, method or type of processing changes, whether separate consent or written consent has been obtained in accordance with the law, and whether exceptions to legal provisions have been met when consent has not been obtained, to ensure that processing activities have a legal basis and fully respect individual wishes.
(2) Processing rules: Focus on reviewing whether the information and contact information provided to the processor are true, accurate, and complete, whether the collected information and its processing methods and types are listed in the form of a list, whether the minimum impact on personal rights is adopted and directly related to the processing purpose, whether the retention period and expiration processing method are clearly defined and ensured to be the shortest time to achieve the purpose, and whether convenient ways to exercise personal information access, copying, correction, deletion and other rights are provided to ensure that the processing rules are transparent, legal, and fully protect personal rights and interests.
(3) Disclosure obligation: Focus on reviewing whether the processing rules are truthfully, accurately, and completely disclosed in a significant, clear, and understandable manner before processing, whether the disclosure text is easy to read, whether the offline and online disclosure methods are effective, whether individuals are promptly notified of rule changes, and whether the non disclosure situation meets the confidentiality or exception requirements stipulated by law, to ensure that the disclosure obligation is fulfilled and the individual's right to know is fully protected.
2. Regarding special handling scenarios
(1) Joint processing and entrusted processing: It is necessary to clarify whether the contract stipulates the respective rights and obligations as well as the supervision mechanism, whether the personal information processor conducts a personal information protection impact assessment before entrusting the processing of personal information, and whether it has a rights protection mechanism and a security reporting mechanism.
(2) Data transfer scenario: If a personal information processor needs to transfer personal information due to merger, restructuring, separation, dissolution, or bankruptcy, the focus should be on examining whether the personal information processor has informed the individual of the recipient's name or contact information.
(3) Automated decision-making: Review the transparency and fairness of automated decision-making, ensure users' right to know, prevent algorithmic discrimination, strengthen user control (refusal, selection) and pre risk assessment, and establish fallback clauses.
(4) Disclosure of personal information: Focus on examining whether there is any abusive behavior (such as sending unrelated commercial information or engaging in online violence), whether the individual's right to refuse is respected, whether consent is obtained when there is a significant impact on personal rights, and whether the scale of processing exceeds a reasonable range; For information disclosed based on personal consent, audits should focus on whether genuine and valid individual consent has been obtained, and whether a personal information protection impact assessment has been completed in advance to ensure that the disclosure behavior is legal, compliant, and respects individual wishes.
(5) Sensitive information processing: Focus on reviewing whether individual consent (or consent from the guardian of a minor) has been obtained, whether the purpose, method, and scope of processing are legal, legitimate, and necessary, whether a personal information protection impact assessment has been conducted in advance, whether the necessity and impact of processing have been communicated to individuals (except for confidentiality situations stipulated by law), whether written consent has been obtained (if required by law), and whether relevant laws and regulations have been complied with to restrict sensitive information processing, ensuring that sensitive information processing activities are legal, compliant, and fully protect individual rights and interests.
(6) Information collection in public places: The focus is on reviewing the legality of equipment installation and information use, including whether it is only necessary for maintaining public safety (rather than for commercial purposes), whether prominent warning signs are set up, and whether individual consent is obtained when using collected personal images or identification information for purposes other than public safety, ensuring that equipment use is legal and compliant and fully respects individual rights and interests.
(7) Under the age of fourteen: The focus is on reviewing whether specialized processing rules have been established, whether minors and their guardians have been informed of the processing purpose, method, necessity, and protective measures (except for those that are not required by law), and whether there is a mandatory requirement for consent to the processing of non essential information, ensuring that the processing of personal information of minors is legal and compliant, and fully protecting their rights and interests.
(8) Cross border transmission: whether key information infrastructure operators have passed the security assessment of the national cyberspace administration; Whether non critical information infrastructure operators have provided non sensitive information to more than 1 million people or sensitive information to more than 10000 people overseas through security assessments; Whether providing non sensitive information to more than 100000 people but less than 1 million people, or sensitive information to less than 10000 people, has passed personal information protection certification or signed standard contracts and filed for record; Whether providing domestically stored information to foreign judicial or law enforcement agencies has been approved by the competent authority; And whether to provide information to organizations or individuals listed in the restricted or prohibited list to ensure the legality and compliance of cross-border data transmission.
3. Regarding the rights mechanism
(1) Deletion right: The focus is on reviewing whether a convenient application acceptance and processing mechanism has been established, whether timely responses have been made and processing opinions or results have been fully and accurately informed, and whether reasons have been explained when rejecting individual rights requests, ensuring that individuals' rights in data processing activities are fully respected and effectively protected.
(2) Timely response: whether an application acceptance mechanism and processing mechanism for individual exercise of rights have been established, whether individual exercise of rights applications have been responded to in a timely manner, whether processing opinions or execution results have been informed in a timely, complete, and accurate manner, and whether reasons have been explained to individuals for refusing individual exercise of rights requests.
(3) Rule interpretation: Whether convenient channels are provided to accept and process interpretation requests, and whether explanations are made in plain and understandable language within a reasonable time to ensure that individuals can clearly understand their personal information processing rules and effectively exercise their rights.
4. Regarding organizational management and internal systems
(1) Internal management: It is necessary to focus on reviewing whether the protection policy complies with regulations, whether the organizational structure is reasonable, whether information is classified and managed, whether emergency response and evaluation systems are established, whether complaint processes and operational permissions are established, whether training plans are developed, whether performance evaluation and illegal liability systems are established, etc., to ensure that the system is sound and effectively safeguards the compliance and security of personal information processing.
(2) Technical and security measures: It is necessary to focus on reviewing whether the confidentiality, integrity, and availability of information are guaranteed through encryption, de identification, and other means, whether the recognizability of personal information is reduced, and whether personnel operation permissions are reasonably set to reduce unauthorized access and abuse risks, ensuring that technical measures match the scale and type of information and effectively protect personal information security.
5. Regarding education and training and job responsibilities
(1) Education and training: It is necessary to focus on evaluating whether safety education and training have been carried out for management personnel, technical personnel, operators, and all staff according to the plan, and to assess the personal information protection awareness and skills of relevant personnel; Simultaneously review whether the training content, methods, target audience, and frequency meet the actual needs of personal information protection, ensuring that the training plan effectively enhances the compliance awareness and ability of all staff.
(2) Personal Information Protection Manager: It is necessary to focus on reviewing whether the person in charge has relevant experience and professional knowledge, is familiar with laws and regulations, whether their responsibilities are clear and they have been given sufficient authority to coordinate internal work, whether they have the right to make suggestions and stop and correct non compliant operations before major decisions, and whether the personal information processor has disclosed the contact information of the person in charge and reported it to regulatory authorities to ensure that the person in charge effectively fulfills their personal information protection responsibilities and promotes corporate compliance management.
6. Regarding Impact Assessment and Emergency Response Plan
(1) Impact assessment: It is necessary to focus on reviewing whether an assessment has been conducted in accordance with the law before handling activities that have a significant impact on individual rights and interests, whether the legality, legitimacy, and necessity of the processing purpose and method have been evaluated, whether the impact on individual rights and interests and security risks have been analyzed, and whether the legality, effectiveness, and risk adaptability of the protective measures taken have been evaluated to ensure comprehensive and effective support for compliance decision-making.
(2) Emergency plan: It is necessary to focus on evaluating whether the plan is based on actual business risk assessment, whether the overall strategy, organizational structure, technical support, and disposal procedures are sufficient to cope with risks, and whether relevant personnel have been trained and regularly practiced; When auditing the emergency response and disposal situation, it is necessary to focus on whether the impact of the incident has been identified and analyzed in a timely manner, whether a notification channel has been established and relevant departments and individuals have been notified, and whether measures have been taken to minimize losses and hazards, ensuring that the emergency plan is comprehensive, effective, and implemented properly.
7. About Internet Platform
(1) Platform rules: It is necessary to focus on reviewing whether the platform rules are consistent with laws and regulations, whether the personal information protection clauses effectively define the rights and responsibilities of the platform and service providers within the platform, and whether the rules are effectively implemented through sampling and other methods to ensure that the platform rules are legal and compliant and effectively protect the personal information rights and interests of users.
(2) Social responsibility: It is necessary to focus on reviewing whether the report fully discloses the following contents: organizational structure and internal management of personal information protection, capacity building, protection measures and effectiveness, acceptance of personal rights applications, performance of independent supervision agencies, handling of major security incidents, promotion of social governance through science popularization and public welfare activities, as well as other legal requirements, to ensure that the report content is true, complete, and reflects the platform's responsibility and effectiveness in personal information protection.
(4) Method
The Cyberspace Administration of China pointed out in its response to reporters' questions regarding the "Audit Measures" that there are no mandatory requirements for how to conduct audits, whether to choose professional institutions, and how to choose professional institutions. Therefore, personal information compliance audit can be mainly divided into two methods: internal audit and external audit.
Internal audit refers to the process where personal information processors can delegate audit work to internal organizations.
External audit refers to the practice of personal information processors entrusting their audit work to external professional organizations for completion. Although the provisions regarding the "recommended directory" have been removed from the official draft of the "Audit Measures", requirements are still put forward for the professional ethics, audit frequency, responsibilities, and obligations of professional institutions.
(5) Third party audit
According to the Audit Measures, personal information processors may entrust professional institutions to conduct compliance audits. The national cyberspace administration and other departments responsible for personal information protection may also require personal information processors to entrust professional institutions to conduct compliance audits on their personal information processing activities. The Measures put forward the following requirements for professional institutions:
1. Professional ethics
Professional institutions should have the ability to conduct personal information protection compliance audits, with audit personnel, venues, facilities, and funds that are suitable for their services. Encourage relevant professional institutions to obtain certification. The certification of professional institutions shall be carried out in accordance with the relevant provisions of the Certification and Accreditation Regulations of the People's Republic of China.
Professional organizations engaged in personal information protection compliance audit activities shall comply with laws and regulations, make professional judgments on compliance audit with integrity, fairness and objectivity, and shall keep confidential personal information, trade secrets, confidential business information, etc. obtained in the performance of personal information protection compliance audit duties in accordance with the law. They shall not disclose or illegally provide them to others, and shall promptly delete relevant information after the completion of compliance audit work.
2. Independent review
Professional institutions are not allowed to entrust other institutions to conduct personal information protection compliance audits. The same professional institution and its affiliated institutions, as well as the same compliance audit leader, shall not conduct personal information protection compliance audits on the same audit object for more than three consecutive times.
(6) Overseas personal information processors
The Audit Measures clearly stipulate that the scope of application is to conduct personal insurance audits within China, seemingly excluding the application to overseas personal information processors. However, due to the extraterritorial application of the Personal Information Protection Law, theoretically eligible overseas personal information processors should fulfill the obligation of personal security audits. According to the relevant provisions of the "Measures for the Protection and Certification of Personal Information for Outbound Personal Information (Draft for Comments)" released by the Cyberspace Administration of China on January 3, 2025, overseas personal information processors who meet the conditions for the extraterritorial application of the Personal Information Protection Law in the future may assist in completing personal insurance audits through specialized institutions or designated representatives established within their territory, or fulfill corresponding compliance obligations through "international mutual recognition".
(7) What companies need to undergo compliance audits?
According to the Audit Measures, this Measures shall apply to the conduct of personal information protection compliance audits within the territory of the People's Republic of China.
Therefore, all "personal information processors" need to undergo compliance audits, but due to the different scales of processing personal information and considerations for potential infringement of numerous individual rights and interests, different personal information processors need to undergo audits at different frequencies, and whether regulatory audits need to be initiated depends on the actual situation.
4、 The Relationship and Difference between PIA and Compliance Audit
As a core tool in the personal information protection system, PIA and compliance audit have both complementary functions and significant differences in implementation logic and scope of action, jointly forming a dual layer defense line for enterprise data governance.
(1) Main associations
1. Goal Consistency: Compliance Assurance and Risk Control
PIA and compliance auditing both aim to promote the legality and compliance of personal information processing activities in enterprises. Through risk identification and control, they reduce the possibility of infringing on individual rights and interests, while also reducing legal disputes or reputation damage caused by violations by enterprises. The two form a complete chain from risk prediction to execution supervision, ensuring the safety and controllability of data throughout its entire lifecycle.
2. Process complementarity: linkage between pre prevention and post verification
PIA is primarily conducted before the start of data processing activities, with the aim of identifying potential risks and recommending appropriate preventive measures to avoid their occurrence. Compliance audit is conducted after the implementation of processing activities to review whether the enterprise has complied with relevant regulations and PIA recommended control measures, in order to ensure the actual implementation effect of preventive measures.
3. Dynamic cycle mechanism for risk management and control
PIA and compliance audit together constitute a continuous risk management process. PIA identifies and evaluates risks in the early stages and develops corresponding preventive measures. Compliance auditing involves checking the execution status in the later stages and may identify new risk points, driving the start of the next round of risk management. This process is a cyclical progression that ensures the continuous optimization of compliance and security in personal information processing activities.
4. Compliance evidence: complementary review basis
PIA report is an important evidence for enterprises to fulfill compliance obligations, detailing the process and results of risk assessment, and providing support for compliance. The compliance audit report further verifies whether the measures recommended in PIA have been effectively implemented by examining whether the actual operations of the enterprise comply with compliance requirements. Both provide sufficient compliance review basis for external regulatory agencies, ensuring the transparency and effectiveness of the entire compliance system.
(2) Core difference
1. Scope of application: PIA focuses on specific scenarios, and compliance audits cover the entire process
PIA is mainly applicable to specific types of personal information processing activities, especially those that may have a significant impact on individual rights, such as processing sensitive data, cross-border data transmission, or automated decision-making. Compliance audit conducts a comprehensive inspection of all personal information processing activities to verify their compliance. Therefore, PIA focuses more on its target audience, while compliance auditing has a broader scope of application.
2. Goal oriented: Forward looking risk identification and post compliance verification
The purpose of PIA is to identify potential risks in the processing of personal information through prospective evaluation and develop effective prevention and control measures to avoid problems in advance. Compliance audit focuses on post audit, checking whether personal information processing activities comply with current laws and regulations, ensuring that the enterprise has not violated compliance requirements in actual operations, and proposing rectification suggestions for compliance issues found.
3. Implementation phase: Pre prevention and post verification
PIA is usually conducted before the start of data processing activities, mainly to prevent risks and help enterprises identify and avoid them before implementation. Compliance audit occurs after a period of data processing activities, mainly reviewing the activities that have been carried out to ensure their compliance and correcting possible illegal issues.
4. Content focus: Differences between compliance verification and risk assessment
PIA focuses on evaluating the compliance of data processing activities, particularly the potential impact on individual rights and whether the protective measures taken comply with regulations. Compliance auditing places greater emphasis on the compliance of actual operations, paying attention to whether every step in the data processing process complies with legal and regulatory requirements, including data collection, storage, use, deletion, etc., and checking whether the enterprise has established an effective compliance management system.
5、 Conclusion
The promulgation of the "Audit Measures" is organically linked with higher-level laws such as the "Personal Information Protection Law" and the "Data Security Law", and complements the refined rules in the industry, constructing a full chain compliance framework covering pre evaluation, in-process control, and post supervision. The new regulations and old laws are interrelated and in dialogue with each other. By clarifying the scope of audit, refining operational procedures, and unifying evaluation standards, the Audit Measures further fill the gap in the institutional connection and practical guidance of personal information protection compliance audit, providing enterprises with a complete standard from principle requirements to specific implementation paths. The formation of this system not only enhances the standardization and operability of corporate compliance work, but also provides institutional leverage for regulatory agencies to conduct penetrating supervision.
Related recommendations
- Tax lawyers review the draft of the revised Tax Collection and Administration Law for soliciting opinions
- New Measures for Punishing "Dishonesty" by the Supreme People's Court at the Two Sessions in 2025 (Part 3): "Height Limit" Single Release Mechanism
- New Measures for Punishing "Dishonesty" by the Supreme People's Court at the Two Sessions in 2025 (Part 2): Grace Period System
- Interpretation of the Management Measures for Compliance Audit of Personal Information Protection - Feeling the Rhythm and Rhythm of Regulatory Flow